The Dutch giant KPN is in the market to stay alive. As the message is now that they are selling E-plus to Telefonica. Consider that the sale of this company is sold for 8 billion, which might seem good. It was however bought a decade ago for 20 billion. So that means a loss of 1.2 billion a year.
So this seems not that good an investment, when you look at it. Is this turning into a moment of selling the family silver cutlery, or is it about more? KPN is not the only one in this regard. Nuon (a Dutch energy provider) is also surfing the red waves of tremendous debt. So much so that its mother company Vattenfal is now putting the Dutch energy giant up for sale. Experts have stated that some of these problems are due to the company holding on to old methods for too long. Considering that they require gas, and the price of gas is up, means that their energy is more expansive then most others.
Back to the Telecoms! In Australia, Vodafone has a multitude of problems. Due to less reliable connection issues they had, over 550 thousand customers left Vodafone Australia for other providers. That is a shift of customers that started only 6 months ago. That means that Vodafone is facing a loss of revenue approaching 20 million a month. So we are talking about a decent amount of revenue. It amounts to a loss of almost 8% of their customer base. That is not even close to the end for Vodafone Australia. They currently have a class action running against them, so that is likely to be a none too small bill, and linked to the loss of customers (at http://www.zdnet.com/au/vodafone-australia-reports-customer-losses-of-551k-7000018290/) we also see that there are currently some legal threats coming from Telstra. That can be read at http://www.zdnet.com/au/telstra-ramps-up-4g-rollout-as-3g-scales-down-7000018225/.
The quote that matters is “Riley also took aim at recent claims from Vodafone that it has better spectrum holdings than Telstra in the capital cities, allowing the company to offer faster 4G services.”
Perhaps Telstra needs to consider a few things!
First there is the article that ABC published in 2011 (at: http://www.abc.net.au/technology/articles/2011/09/28/3327530.htm).
Yes, I got to hear all about it in Uni when I was doing my mobile technologies subject (party of my IT degree), so if this is about ‘marketing’ claims, then Telstra might revoice the words stated in the claim. They could read the following: “Riley also took aim at recent claims from Vodafone that it has better spectrum holdings than Telstra in the capital cities, allowing the company to offer faster 4G services” in the air of “Riley is also aiming at the mention that Vodafone is more colourful then Telstra when offering a mobile service labelled as 4G in the capital cities“. Have you seen those BORING 4G posters all over Sydney? Yup, making legal threats against opinions, that makes perfect sense to me…..NOT!
OK, it is 2013 now and there are true 4G providers now, but what is important?
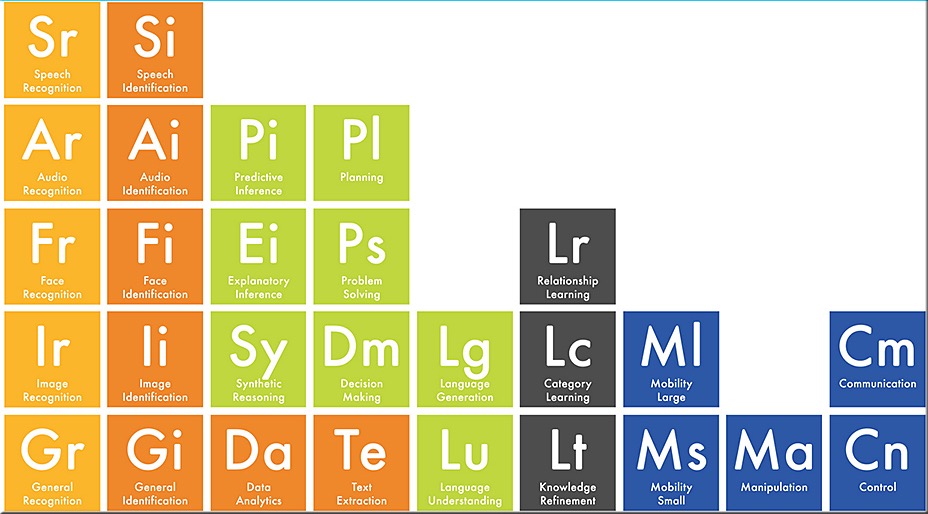
4G is the fourth generation of mobile phone mobile communication technology standards. (Quick Wiki grab). When we consider the 4th generations, we see WiMAX and we see LTE (Long Term Evolution). The ITU (International Telecommunication Union) stated the requirements on what makes a 4G standard. So when the International Mobile Telecommunications Advanced (IMT-Advanced) specification was set for the 4th generation in 2008, there was an actual next generation target to achieve. You wonder why it took so long? Well, the ITU looks forward on what the next step would be. So they set peak speed requirements for 4G service at 100 megabits per second (Mbit/s) for high mobility communication (such as from trains and cars) and 1 gigabit per second (Gbit/s) for low mobility communication (such as pedestrians and stationary users). This would indeed be a massive step forward in a time when those speeds were not even close to an option. It makes perfect sense. You have seen this before. When we went from VHS to DVD, similar steps forward were made. This step was even larger as people moved from DVD to Blu-Ray.
It is technical evolution baby!
Yet, Telco’s are all about marketing, and Telstra was really clever. From the information that WAS then, they basically offered 3G+ and named it 4G, but that does not make it true 4G. That is how I personally see it! When I think of a power Telco offering 4G, I think of NTT DoCoMo and TATA (India). DoCoMo has close to 60 million customers in Japan, which is well over 45% of the mobile user population. How many Telco’s can actually make the claim that 1 in 2 connects to them in the Mobile community? In India there is the Tata Teleservices group with over 75 million customers, and NTT DoCoMo owns 25% of this.
So when we think Telco, Telstra and Vodafone Australia do not really measure up. Yet the interesting link here is that NTT DoCoMo had Billions invested all over the world, including in KPN in the Netherlands. Is it not interesting to see how these Telco’s seem to cross pollinate? This raises an issue that many people forget. If we consider the Vodafone class action, and if we consider the reasons of bad connections, then what is going on? Our little Island has 20 million people, which is less than a third of the active Japanese mobile phone users. So why are our connections failing (I am only considering the large cities)? It is clearly not about technology, but about infrastructure and implementation (in my humble view). Yes, we should not forget costing here either, as it all costs money, but consider the income in India and Japan, consider the amount of users. NTT ended up with a net income (after expenses and licenses) of roughly 5 billion dollar last year, which is almost 12% of the total revenue. So we see three things.
1. A ROI of 12% is not that bad.
2. Several nations are competing against giants with means we cannot fathom.
3. All of them seem to be writing off ‘losses’ on massive levels.
Is this about losses, about write offs or about something that is not here?
I reckon it is mostly about the not being there bit. When we look at incomes then we see that the Vodafone Europe CEO (Vittorio Colao) made 2.2 million Euro, whilst David Thodey, CEO of Telstra makes a mere 7 million dollars. So, yes they make decent coin, yet nothing more a mere mid-level banker is likely to get as an annual bonus, so the money is not draining away in that direction either.
No, I personally see the issues as a side effect of devaluation of technology. This is a side that has been ignored by most members of the public from 1997 onwards. You see, technology providers saw the benefit of the armistice race and went the same way. Every year we see a PC, laptop or tablet that is better, faster and newer, but how much faster? The impact with computers is not that big as it hits the individual. They deal with slightly larger programs, and that is pretty much it. Your text file is not that much larger. If you consider a 3000 word document, then that file remained relatively the same over the last 10 years. For electronic devices like TV’s it is also the same. We get the same signal and beyond that it only looks nicer, all this did not impact the provider.
With telecom it’s a different cattle of fish (pun intended). When we upgrade our phones we also attach to that an almost exponential growth of data needs, as such as Apple sold around 25 million mobile phones per quarter, we see that the need for an almost exponential growth of infrastructure is needed (a lesson Vodafone is learning the hard way). Even as the large Telco’s are installing the need for hardware on a continuing base, and as we see the replacement of equipment, we see that the life time of current facilitating hardware is likely less than 40% of its actual life cycle. It is either that of build more places with facilitating equipment, with a connected drain of ‘revenue left’ as well. The last level is one that is not that apparent at present, but will hit Telco company values on a massive scale soon enough. This side can be read at http://www.globallegalpost.com/blogs/global-view/registered-patents-devalued-by-outdated-ip-laws-6786253. Considering the issues at play, then the assets of Telco companies are about (read 2-4 years) to hit a certain basement value. I reckon that there will be consequences down the road. In my view it will be that the truly big boys will continue, the smaller packs will no longer be able to compete in a field where they will get charged for services needed and then some.
What is the solution? Not sure, it is in the end a business answer. Yet, voicing a 1.2 billion loss a year cannot be that good for the ego, and as the amount of players increase, these levels of ‘bad’ news will continue. It will not hit your taxes, but consider that services falter, where will you run to when your mobile phone leaves you with the message ‘searching…’ from your provider?