Yup, we all have a stage when there is no trust, there is no confidence and we wonder the why part. In this, I had questions, so I asked the agency, but they did’t know, then I asked the FBI, I asked Langley and I asked Commander Andrew Richardson, they all gave the same story, there is No Such Agency, so I Googled them and Yes! There they were, complete with phone number (+1 301-677-2300) and all, yup, we got them, so now we get to their story (at https://breakingdefense-com.cdn.ampproject.org/c/s/breakingdefense.com/2021/04/nsa-about-to-release-unclassified-5g-security-guidance/amp/).
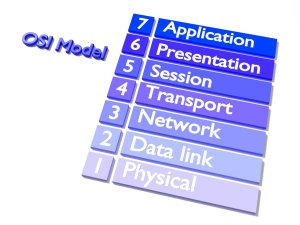
Via the BBC, we get ‘NSA About To Release Unclassified 5G Security Guidance’ and I started to read, the article makes a lot of sense. Which gave me “Noble’s speech highlighted the importance of zero-trust architecture in 5G networks”, and it got me thinking, the approach makes a lot of sense, just like SE-LINUX, the setting of ‘no-trust’ makes sense, especially in a world where Microsoft keeps on fumbling the ball, not merely their exchange servers, but the (what I personally see as greed driven) push towards Azure, it comes with all kinds of triggers and dangers, especially as they are ready to cater to as many people as possible, the no-trust rule is pretty much the only one that makes sense at present. I have written about the dangers more than enough. So when we are given “it’s reasonable to expect that future NSA 5G security recommendations will emphasise zero trust as a key component”, I believe that the approach has a lot of benefits, especially when such a setting can be added to anti viral and Google apps, it could increase safety to well over 34% overnight, and option never achieved before and we should all applaud such a benefit. There are a few thoughts on “NSA has characterised zero trust as “a security model, a set of system design principles, and a coordinated cybersecurity and system management strategy.” It’s a “data-center centric” approach to security, which assumes the worst — that an organisation is already breached or will be breached.” A choice that is logical and sets the cleaning directly at servers and ISP’s, and they are the backbone in some cases to close to 75% of all connections, so to set a barricade on those places makes sense, there is no debating, the choice of calling themselves No Such Agency wasn’t their best idea, but this is a game changer.
I have been critical of the US government in all kinds of ways for years and on a few topics, yet I have to admit that this is an excellent approach to prevent things going from bad to worse, moreover, there is every chance that it will make things better for a lot of us overnight as such a system deploys, it will have a trickle down effect, making more and more systems secure.
That one thing
Yup there is always one thing and we see the dangers when we consider Solarwinds and Microsoft (their mail server), the one part is when we rely on rollbacks and we see rollback after rollback creating a hole and optionally a backdoor, the most dangerous system is the one deemed to be safe, ask Microsoft, or their exchange server. When you believe all is safe, that is when the most damage can be made. And as the article looks at 4 parts, we see ‘Improved network resiliency and redundancy’, yes it makes sense, but rollback efforts are possibly out of that equation and when we get some people tinkering there, there is a chance that the solarwinds paradox returns, yet this time with a dangerous seal of approval by the No Such Agency, it will be the one part all criminal minds are hoping for, in this I personally hope they fail, but these buggers can be resilient, tenacious and creative, the triangle that even the Bermuda Triangle fears and that is saying something.