Yes, that was the setting I gave you yesterday and in good standing I used the absolute worst application of latin you see here. (Planking the read), which roughly (really roughly) translate to a ‘reading plank’. I know I have a seriously warped sense of humor. You see it was important to do this in latin, because other languages have 10 of thousands of words. In Latin the idea is a little far fetched, but still applicable.
So as such I got these 20 words to start of with:
Aqua (water) Asini (donkey) Aquilla (eagle) Pratus (meadow)
Triticum (wheat) Equos (horse) Columba (pigeon) Virgo (maiden)
Solum (soil) Currus (chariot) Cervus (stag) Sarcedos (priest)
Germana (sister) Via (road) Serpens (snake) Templum (temple)
Germanus (brother) Fluvius (river) Aper (boar) Vinum (wine)
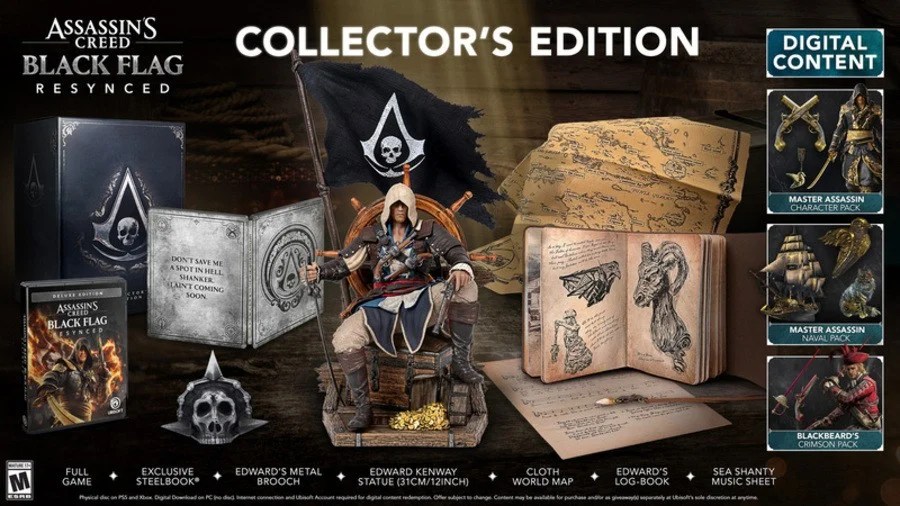
So from there I started to think, these reading planks are static, the internet is not, so the idea came to me to upgrade the plank to the next level. When you get 100% on these words the plank will ‘upgrade’ to the next level, but it will not happen too soon. You see, the plank is also a gateway to lessons. A lesson on family (brother/sister) a lesson on animals (donkey/horse) a lesson on priest and temples and so on, only when you passed them all you get the next level of a reading plank. There will be a lesson on the hunt (boar/stag), lessons on transportation (horses/chariots) and this is another way to learn language, but as I see it, the approach will translate to Italian, Spanish, French and German in almost the same way, as I see it, the setting is almost transferable, not completely though, because the scenery will be different and the changes will be seen almost all over. The idea to have the plank and stick the work (which are on parchment) on this. As I see it, there are two ways to get into the Latin game and both are open. The first is a ‘poor’ serf who becomes a serf serving a priest in Rome (AC Brotherhood)

As you see, it is only part of the map, it includes the Vatican and part of Rome. As a Papal guard you can enter the Vatican and you get a dwelling on Vatican island. As a serf you get a room in the church of the priest you serve and over time you will be allowed and required to enter Vatican island. Both will introduce you to etiquette and interactions with people both are different in the interactions whilst the priests will interact with the guards, as a serf you can only do the bidding of the priest and the jobs given. You can still interact with the people in Rome. As I see it a rather large linguistic challenge awaits you and the setting is almost the same for Italian, although you are nearly always housed in Rome, but as you gain experience and become adequate in Italian, you could meet and interact with people on Vatican Island, but the priests and cardinals there will only address you in Latin (unless you are given a job to do something in the Vatican).You think this is shallow, but etiquette mattered in those days and don’t think you can throw your weight around. The papal guards are not the nicest people to be rude to and at that moment you get a time out from the game and you are given clear instructions (in your dwelling) and you get to practice there for about an hour to get you more proficient in Italian and manners.
This is merely your the beginning of what comes the way of the linguistically student. You see, it is not enough to merely learn the language, you will be pushed to get a feel for the language, something you could never get being the Apfelkorn jerk in Cortina d’Ampezzo. But as I see it, this is the way that could also be used to teach English and that too has two versions (and you would get both versions) the ‘proper’ way from AC Syndicate giving you class lessons and well (Whitechapel, The Strand, The Thames, The City of London and Westminster) and you get to learn the language skills and the etiquette as was custom in Victorian England. Modern day England is in Watchdogs Legion around Big Ben. French is in Paris (AC Unity) and Arabic/Farsi is in AC Mirage and Japanese/Portuguese is in AC Shadows. The materials are largely done (by Ubisoft) they merely need to reset the maps to the language areas and add the vocal part, the games and the tutelage parts. As I said, Ubisoft starts with a 75% program,
I wonder which languages AC Hexe adds to the equation, I think it was German. Whatever you might think is valid but I wonder if Ubisoft had any idea what more was possible on products they had already finished. And that is before you consider how engaging the language becomes when this is paired with a meta quest visor.
Have a great day