I saw an article at the BBC and I will get to that in a moment, but it reminded me of a situation that happened in 2010. I needed a new laptop and I was looking in a shop at their Collection of laptops. A man came to me and was trying to convince me just how amazing this laptop was. My inner demon was grinning, I get it, the man was enthusiastic, he was giving the numbers, but in all this, did he realise what he was saying? I am not doubting the man’s skills, he was doing a good job, I was however in IT and had been there for 30 years, so I have pretty much seen it all, and there it was, my little demon, on my right shoulder calling me ‘pussy’. So as the man stated ‘this laptop has a one terabyte hard-drive, can you even imagine ho much that is?’, I could not resist and my response was ‘Yup, that would fit roughly 10% of my porn collection’, his jaw dropped to the ground, his eyes almost popped, the demon inside me stated ‘Nice!’ Actually, it was not quite true, it would only fit a rough 0.32114%. It was the impact of the shock factor. You see, there is a hidden agenda there, when you (appropriately) use the technique, you get to see the real salesperson and that was what I needed. He was thrown, but he recomposed and continued giving me the goods on the laptop, I bought that laptop roughly 132 seconds later.
So today I saw ‘The Rise of extortionware’ (at https://www.bbc.com/news/technology-56570862), here I notice “where hackers embarrass victims into paying a ransom”, it is not new, it is not even novel. I will also give you the second game after the people involved get arrested, they will demand anonymity and any bleeding heart judge will comply. I state that these people will be handed the limelight so that the people that faced ransomware attacks can take their frustration out of these people. But that remains wishful thinking. So next we get “Experts say the trend towards ransoming sensitive private information could affect companies not just operationally but through reputation damage. It comes as hackers bragged after discovering an IT Director’s secret porn collection.” I have the question was it a private or a company computer? You see, sone focus on the boobies, just what the advertisers on Twitter hope for, they want the click bitches, it makes them money. It is time that we set the larger stage, you see the entire mess would be smaller if Cisco and Microsoft had done a proper job. OK, I apologise, Cisco does a proper job, but some things slip through and in combination with Microsoft exchange servers it is not slipping through, it is a cyber hole the size an iceberg created on the Titanic and we need to set a much larger stage. So when we see “Thanks God for [named IT Director]. While he was [masturbating] we downloaded several hundred gigabytes of private information about his company’s customers. God bless his hairy palms, Amen!”, it seemingly answers that he might keep it on a corporate computer, or he uses his private computer for company stuff. Yet in that same light the hacker should not be allowed any anonymity, we all get to see who the hacker is. If there is something to be learned it is see with “Hackers are now actually searching the data for information that can be weaponised. If they find anything that is incriminating or embarrassing, they’ll use it to leverage a larger pay-out. These incidents are no longer simply cyber-attacks about data, they are full-out extortion attempts” There are two sides
- The station of ALWAYS ONLINE needs to change, there needs to be an evolving gateway of anti hack procedures and a stage of evolving anti hack routers and monitoring software. You think that Zoom is an option?
Tom’s Guide gave us less than 2 weeks ago “More than a dozen security and privacy problems have been found in Zoom”, as well as “Zoom’s ease of use has made it easy for troublemakers to “bomb” open Zoom meetings. Information-security professionals say Zoom’s security has had a lot of holes, although most have been fixed over the past few year”, so whilst you contemplate ‘most have been fixed’, consider that not all are fixed and that is where the problem goes from somewhat to enormous. Well over 20% of the workforce works at home, has zoom meetings and that is how cyber criminals get the upper hand (as well as through disgruntled employees), a change in mindset is only a first station. - Remember that Australian? (Julian Assange) We were told that soon there would be some leaks on issues on banks (Wall Street) then it suddenly became silent, now some will say that it is a bluff, but in light of the meltdown in 2008, I am not so certain, I reckon that some have ways to show the hackers who they are and they profit by not doing that. Can I prove this? Absolutely not. It is speculation, but when you look at the timeline, my speculation makes sense.
- The third side is optionally the second side as the second side might not be a real side. When we see “Hackers are now actually searching the data for information that can be weaponised. If they find anything that is incriminating or embarrassing, they’ll use it to leverage a larger pay-out. These incidents are no longer simply cyber-attacks about data, they are full-out extortion attempts”, the underlying station is ‘information that can be weaponised’ and the IT sector is helping them.
How did I get there? The cloud is not as secure as some state, and the salespeople need to take notice. Business Insider gave us about 6 months ago “70% of Companies Storing Data With Cloud Companies Hacked or Breached”, see the link we are now slowly getting presented?
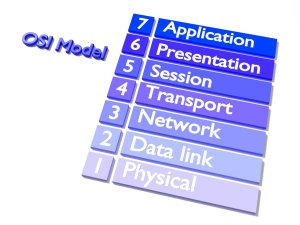
In the OSI model, we see layers 3-7 (layer 8 is the user). So as some have seen the issues from Cisco, Microsoft and optionally Zoom, we see a link of issues from layer 3 through to layer 7 ALL setting a dangerous stage. Individually there is no real blame and their lawyers will happily confirm that, but when we see security flaw upon security flaw, there is a larger stage of dangers and we need to take notice. And here the dangers become a lot more interesting when we consider the Guardian yesterday when we saw “Intelligence value of SolarWinds hacking of then acting secretary Chad Wolf is not publicly known”, what else is not publicly known? How many media outlets ignored the Cisco matter, how come ZDNet is one of the few giving us “it’s not releasing patches for some of the affected devices that reached end of life” less than 8 weeks ago. Again I say Cisco did the right thing by informing its customers close to immediately, yet when we see “More than 247,000 Microsoft Exchange servers are yet to be patched against the CVE-2020-0688 post-auth remote code execution (RCE) vulnerability impacting all Exchange Server versions under support” (source: bleepingcomputers.com) as far as I can see, a lot of the media ignored it, but they will shout and repeat the dangers of Huawei, without being shown actual evidence, and I state here, that unless we make larger changes, the extortion path will evolve and become a lot larger. With 70% of cloud systems getting hacked or breached, a large chunk of the Fortune 500 will pay too much to keep quiet and who gets to pay for that? There is a rough 99.867765% chance that its board members will not, it might be speculatively, so please prove me wrong.
A stage where the needs of the consumers changes in a stage where the corporations are not ready to adjust and all whilst the IT salespeople have that golden calf that does everything and make you coffee as well. Adjustments are needed, massive adjustments are needed and we need to make them now before the cybercriminals are in control of our IT needs and that is not mere speculation, when you see flaw after flaw and too little is done as too many are the victim of its impact is a serious breach and it has been going on for some time, but now it is seemingly out in the light and too many are doing too little and as we laugh at “God bless his hairy palms, Amen!” Consider that stage, and now consider that they invade a financial institution, these are clever criminals, they do not empty your account, they merely take $1, perhaps $1 every other month, this implies that they are looking at a $16,000,000 every two months. And this is merely one bank, one in a thousand banks, some a lot bigger than the Australian Commonwealth bank and lets face it, the fact that layer 3 to layer 7 is leaky in hundreds of thousands of customers, do you really think that banks are off-limits? Do you really think that this is a simple hick-up or that the scenery is changing this quickly by people claiming that it will be fixed in no-time?
We need massive changes and we need them a lot sooner than we think.